The Attack That Got Us to This Point and the Next One Coming
The Attack That Happened
Email continues to be a primary driver in my work life. As a Gen X person, I expect to primarily use email for my entire adult working life; I will have an inbox as long as I continue to receive a paycheck. In the past five years, I have twice—that I know of—received email messages impersonating my boss at one of my clients, directing me to send money somewhere or change a password on an account. I almost did the requested thing because the email was worded decently but then thought, “Hmm. I think my boss would have called me with a request like this or would have sent it via Slack. Is this a scam?” Yes, that happened.
A few years ago, maybe a year and a half before COVID, that same company was hit by a ransomware attack. The servers at the office were toast. The ransomware came via email. Someone clicked a bad link and the next morning: Flatline. The IT admin had turned everything off to stop the spread any further. For a few weeks, email was banned; we could only communicate with each other via Slack or phone. Before the attack, the company had a rough plan to move their on-prem servers and software to the cloud. The ransomware attack significantly accelerated the company’s plan to move to the cloud. Now, only one server remains at the office. It has a VPN connection, and someone must turn on the FTP connection to receive large files from customers. The FTP connection then gets turned off after files are moved. For everything else, they’re 100% in the cloud.
The Attack That Might Come Next
I recognize that although the cloud is more secure, I expect another ransomware attack (or similar) will happen in the future. Something will hack their business environment in the cloud. We all need better tools and more training to be ahead of the next attack.
I’ve read many articles and blogs and watched many videos indicating that we’re just at the very beginning of AI and imagining how it will impact our business lives. As an analogy, while we’re using ChatGPT, DALL-E, and Copilot today, we’re basically where we were in the late 90s using cell phones to make phone calls and write text messages using T9Word. As far as I know, nobody has yet created something in AI that’s the equivalent of Apple introducing the first iPhone where suddenly the world of software does a massive evolution. I remember the realization when the basic function of a phone in my pocket became a device where I have my calendar, I do most of my reading, and I trust it to navigate me to unfamiliar locations. Remember when companies like Microsoft declared that almost all of the software they build from that point forward will be “mobile first?” We’re nearly there with mobile. We are not there yet with AI, but I can see it coming.
I recognize that AI technologies will have a huge impact on everyone’s lives. Most people will individually choose to use AI-powered improvements for “good things” that generally befit and automate their lives. But AI improvements will also give bad actors better tools to do bad things. Something bigger and worse than clicking an email link and taking down a company’s internal servers may happen in a way that touches each of us.
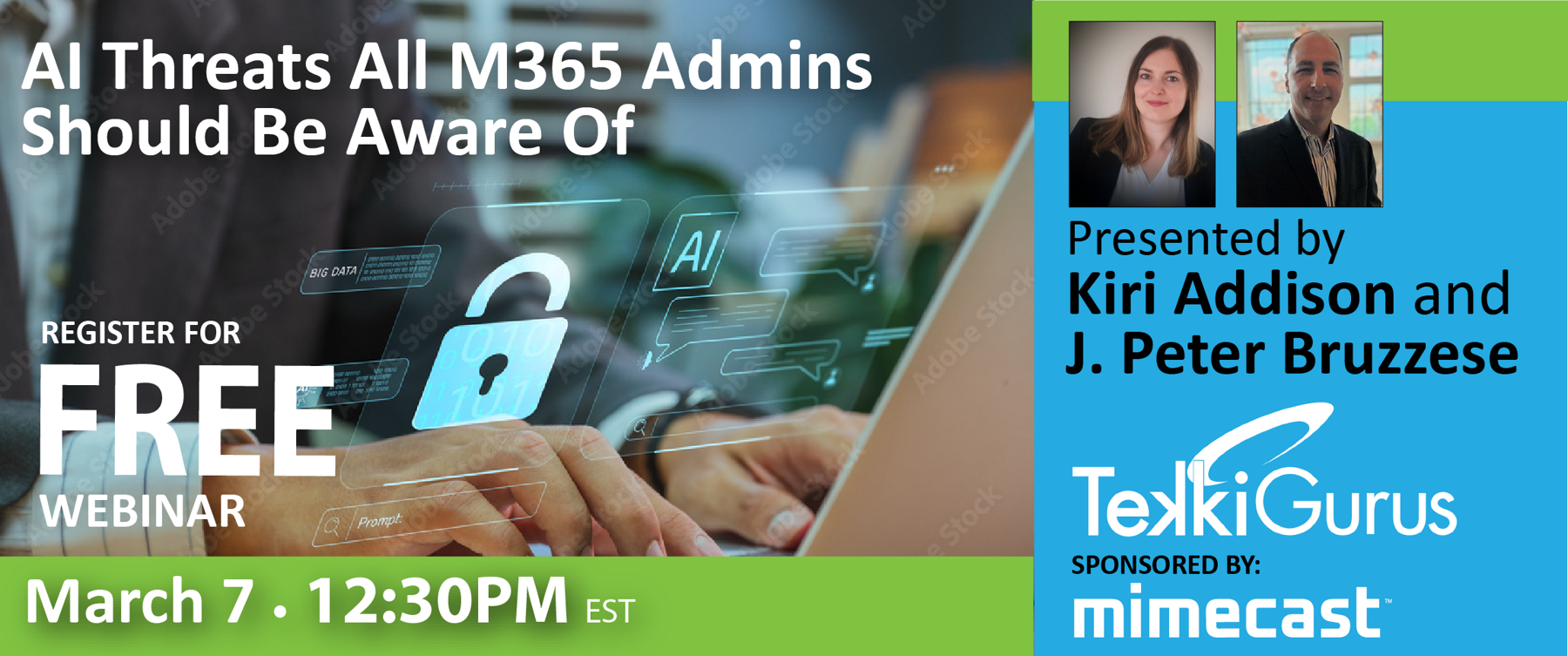
On March 7, 2024, TekkiGurus and Mimecast will work together to produce one of the best webinar topics I think I’ve seen, AI Threats All M365 Admins Should Be Aware Of. I’ll be in the audience for that webinar. In a different work capacity, I’m also an M365 admin. I know enough to create and disable accounts, deal with billing, and help others install software. Why am I an admin? I’m trusted and cautious, but I’m not sure I’ll know what to do when AI-powered tools allow a hacker to make a Teams call to me and credibly impersonate my boss. I am sure that I don’t know—right now—what to do when the next bad email gets through and a bad link takes down a tenant.
Articles that I’ve read from security experts suggest that a combination of better software and better planning plus company policies to get ahead of the next hack is a good investment of money and time. Tools that Mimecast develops and sells are the kinds of tools I expect many companies should use, and they might have prevented that ransomware attack back when. I think it took almost two years from the date of the ransomware attack to get to the point where they were done with it. The company lost data that they’ll never recover. I’m sure the costs exceeded $250,000. The company had insurance to offset the expenses of a cyberattack, but not the time it took everyone to deal with it. I feel more secure now that they’re in the cloud, but I cannot keep up with the bulletins released by the Microsoft Security Response Center; my vision starts to glaze over when I read about the next security settings I should change or the next tool that Microsoft Security has introduced or renamed. I expect that the security defaults in M365 are better than what they had when there were servers at the office, but it’s wiser to layer on better security rather than sticking with the defaults. I expect to learn about that in this AI Threats All M365 Admins Should Be Aware Of webinar. I also expect that the IT person who guided that company through the last ransomware attack may retire. They’ll lose that institutional knowledge and have to start from scratch. Webinars like this one can help all of us be better prepared.
Read the webinar description. I hope you learn from it. If you cannot make the live presentation, please watch the recording.